Security Architecture
Security is not a badge. It’s a blast radius.
Designed for low-friction pilots. Built to pass deeper reviews as we scale.
Secure document review environment
Flightline operates as an isolated review portal. Loan files are analyzed in a contained environment, separate from your production systems.
Authenticated portal access
Loan files are uploaded through authenticated sessions. No direct integration with your LOS or core banking systems.
No system connections
No inbound system connections. No outbound system dependencies. Your infrastructure stays untouched.
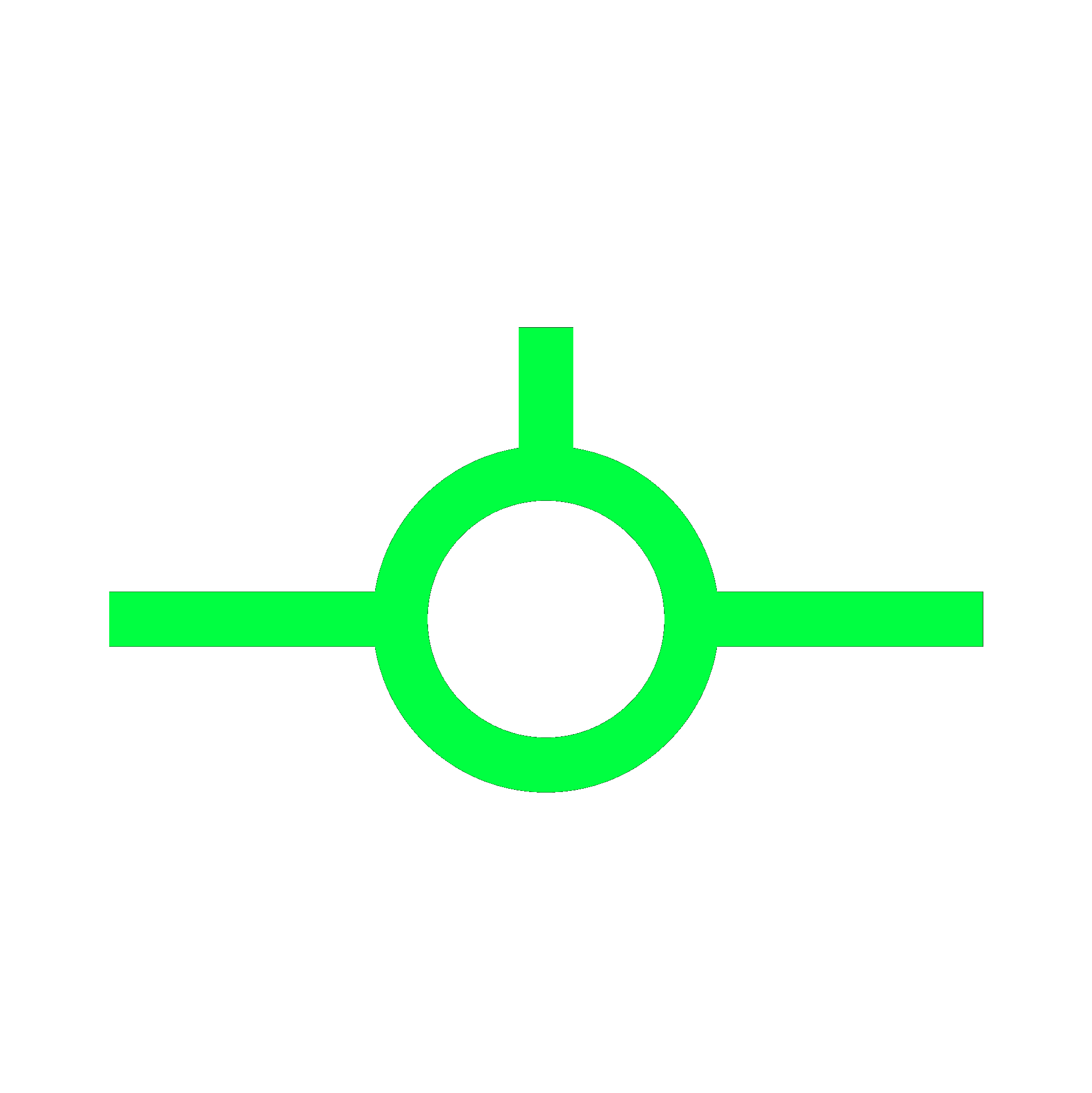
Authenticated user uploads file package
Files stored in encrypted object storage
Documents parsed and analyzed
QC report generated
Archive retained per configured retention policy
No inbound system connections. No outbound system dependencies.
Because Flightline is not connected to core systems, it cannot:
Organization-level tenant isolation
Each organization operates in a fully isolated tenant. No data crosses organizational boundaries.
Role-based access controls
Users see only what their role permits. Permissions are explicit, not inherited.
MFA enforced
Multi-factor authentication required for all user accounts. No exceptions.
All user activity logged
Every document access event is logged. Every finding includes a timestamp and user context.
Immutable review records
Once a review is archived, the review record cannot be altered. Full audit trail preserved.
Built for regulated environments from day one.
Small attack surface. Isolated deployment. No system entanglement. Security through architecture, not paperwork.
View our Trust & Compliance portalWhere is data stored?
Encrypted object storage in cloud infrastructure with access controls at every layer.
Who can access it?
Only authenticated users within your organization's tenant. Role-based permissions control visibility.
Is data used for training?
No. Customer data is never used to train models.
Can we control retention?
Yes. Retention policies are configurable per organization.
What happens if we terminate?
All data is purged according to your retention policy. Nothing persists after termination.